74 KiB
The Surreptitious Assault on Privacy, Security, and Freedom
Remember the themes!:
- Surreptitious
- User privacy and security
- Affects on freedom; chilling effects
- How free software can help
The big players seem to be the Web and Government. No surprises there.
It would be a good idea to immediately connect with the audience. So:
-
Most everyone has a mobile device.
- This is the most immediate and relatable since it's physically present with them in their travels.
- Security cameras et. al. during travel.
So start briefly with the topic of pervasive surveillance?
- That is what the abstract refers to, after all.
Surreptitious—many audience members won't consider that they're being tracked.
- But by whom?
Maybe a gentle introduction that gets increasingly more alarming and invasive topic-wise.
LaTeX Configuration export ignore
% citations will be grayed and pushed to the right margin ≤t\origcite\cite % incite = "inline" cite \def\cite{\hfill∈cite} ≠wcommand*{∈cite}[1]{{% \scriptsize \raisebox{1ex}{% \color{gray}% \origcite{#1}% }% }}
\renewcommand*{\bibfont}{\scriptsize}
Slides export ignore
Development Notice B_fullframe
N.B.: These slides appear as they were presented at LibrePlanet 2017 (with the exception of this slide).
For up-to-date slides, see:
For the source code to this presentation, see:
Introduction / Opening B_fullframe
Hello, everyone. Thanks for coming!
My name's Mike Gerwitz. I am a free software hacker and activist with a focus on user privacy and security. I'm also a GNU Maintainer, software evaluator, and volunteer for various other duties.
And I'm here to talk to you about an unfortunate, increasingly unavoidable fact of modern life.
None of you made it here without being tracked in some capacity. Some of us are still being tracked at this very moment!
This isn't a tinfoil hat presentation. It's a survey of facts. Every slide has numeric citations, which are associated with references on the final slides. I won't be showing them here—you can get them online. Since time isn't on my side here, I'm going to present a broad overview of the most pressing concerns of today, as it hopefully relates to everyone here. My goal is to present you with enough information that you know that these things exist, and you know where to find more information about them. Those unknown unknowns.
So: let's start with the obvious.
(Note: You're being "tracked", rather than "watched": the latter is too often used and dismissed as tinfoil-hat FUD.)
Mobile [5/5]
Introduction B_ignoreheading
Introduction B_fullframe
- <1-> Most people carry mobile phones
- <1-> Synonymous with individual
- <2> Excellent tracking devices
Most of us in this room are probably carrying a mobile phone right now. They are computers that are always on.
A phone is often synonymous with an individual; they are a part of us— we feel incomplete when we're missing our phones. In other words: they're excellent tracking devices.
Cell Towers [6/6]
Fundamentally Needed
Summary
- Phone needs tower to make and receive calls
- Gives away approximate location\cite{pbs:nova:boston}
- Multiple towers: signal delay; triangulate
Tower Image

∈cite{w:file:cell-tower}
The primary reason is inherent in a phone's design: cell towers. A phone "needs" to be connected to a tower to make and receive calls.
Unless it is off or otherwise disconnected (like airplane mode), its connection to the cell tower exposes your approximate location. If the signal reaches a second tower, the potential location can be calculated from the signal delay. More towers, you can also triangulate.
Some people don't use phones primarily for this reason.
rms, for example, said he might use a phone if it could act as a pager, where he'd only need to expose his location once he is in a safe place.
Cell-Site Simulators
Summary
- <1-> IMSI-Catchers
- <1-> Masquerade as cell towers
- <1-> Most popular: Stingray
- <2-> Free/libre Android program AIMSICD available on F-Droid attempts to detect\cite{aimsid}
Stingray Image

∈cite{w:file:stingray}
Cell Site Simulators have made a lot of news in the past, one of the most popular examples being the Stingray. These devices masquerade as cell towers. This allows (for example) law enforcement to get a suspect's phone to connect to their device rather than a real tower, which allows their location to be triangulated, calls to be intercepted, etc. Law enforcement might also use it to record all devices in an area, such as during a protest.
The problem is: every phone in the area will try to connect to it; it amounts to a dragnet search, and is therefore extremely controversial.
The Android program AIMSICD—Android IMSI-Catcher Detector—is being developed in an attempt to detect these devices. It is free software and is available on F-Droid.
Verizon Metadata (Order) B_fullframe
 \par∈cite{archive:fisa-verizon}
\par∈cite{archive:fisa-verizon}
Anyone remember this?
This is the first Snowden leak— the secret FISA court order that renewed the FBI Verizon metadata collection program.
For those who may not know: FISA is the Foreign Intelligence Surveillance Act, and it established a secret court that usually also issues gag orders.
Ron Wyden B_fullframe
Senator Ron Wyden, 26 May 2011:
I have served on the Intelligence Committee for over a decade and I wish to deliver a warning this afternoon. When the American people find out how their government has secretly interpreted [the business records provision of FISA], they are going to be stunned and they are going to be angry.\cite{eff:jewel:evidence}
Verizon Metadata
- <1-> June 2013—Guardian releases leaked document ordering Verizon to collect ``telephony metadata''\cite{guardian:verizon,mtg:uproar}
[…] (i) between the United States and abroad; or (ii) wholly within the United States, including local telephone calls.\cite{archive:fisa-verizon}
- <2-> Routing information, source and destination telephone numbers, IMSI and IMEI numbers, and time and duration of the call\cite{archive:fisa-verizon,eff:metadata}
- <3-> ``Business records'' provision partly declassified by Clapper on 6 June 2013\cite{dni:business-provs}
- <3-> The American people were stunned and angry
June 2013. I remember where I was.
The Guardian newspaper releases a leaked court order, which orders Verizon to collect ``telephony metadata'' on all calls, including domestic.
These matadata include <read above>.
That ``business records'' provision of FISA that Ron Wyden was talking about was partly declassified by the then-DNI James Clapper shortly after that publication.
As Wyden predicted, we were pretty stunned. And pretty pissed off.
Metadata Matters
 ∈cite{eff:nsa-spying}
∈cite{eff:nsa-spying}
-
EFF on ``Why Metadata Matters'':\cite{eff:metadata}
- <2-> They know you rang a phone sex service at 2:24 am and spoke for 18 minutes. But they don't know what you talked about.
- <3-> They know you spoke with an HIV testing service, then your doctor, then your health insurance company in the same hour. But they don't know what was discussed.
There was a debate over how much ``metadata'' matters. It matters a lot.
Here's some quotes from an EFF article, as cited.
<Read quotes>
Metadata are important.
Wifi [1/1]
ESSID and MAC Broadcast
- <1-> Device may broadcast ESSIDs of past hidden networks
- <1-> Expose unique hardware identifiers (MAC address)
-
<2-> Defending against this is difficult
- <3-> Turn off Wifi in untrusted places
- <3-> Turn off settings to auto-connect when receiving e.g. MMS
- <4-> Use cellular data (e.g. {2,3,4}G)
- <5-> **MAC address randomization works poorly**\cite{arxiv:mac}
What else is inherent in a modern phone design? A common feature is Wifi.
If you connected to any hidden networks, your phone may broadcast that network name to see if it exists.
It exposes unique device identifiers (MACs), which can be used to identify you.
Defending against this is difficult, unless you take the simple yet effective route: disable Wifi completely, at least when you're not in a safe area you can trust. Some apps will automatically enable networking if they receive, for example, MMS messages; be careful of that. If you really do need data, use your cellular data. You are already hemmoraging information to your phone company, so at least you're limiting your exposure.
Some phones and apps offer MAC address randomization. That's a good thing in priniciple. Unfortunately, it seems to be easily defeated. One study, cited here, claims to be able to defeat randomization 100% of the time, regardless of manufacturer.
Segue to next section: All these previous risks are passive— they require no malicious software on your device. But what if we do have such software? And of course, we do.
Geolocation [3/3]
Global Positioning System (GPS)
 ∈cite{w:file:gps}
∈cite{w:file:gps}
- <1-> Not inherently a surveillance tool
-
<2-> Often enabled, and programs abuse it\cite{jots:mobile}
- <2-> Legitimate: navigation, social media, photos, nearby friends, finding lost phones, location-relative searches, etc.
- <3-> If phone is compromised, location is known
Let's talk about geolocation! The most obvious being GPS.
GPS isn't inherently a surveillance tool; it can't track you on its own. Your GPS device calculates its location based on signals broadcast by GPS satellites in line-of-site.
It's often enabled on devices, and programs often abuse that privilege.
I'm not saying there aren't legitimate uses. Navigation systems, location-relative searches, finding lost phones— all of these things are legitimate.
But I Want GPS!
-
<1-> Is the program transparent in what data it sends? (Is the source code available?)\cite{jots:mobile}
- <1-> 2010: 47 of top 100 Android and iOS apps sent location to devs and third parties\cite{wsj:app-loc}
- <1-> Ex: Angry Birds sent address book, location, and device ID to third party\cite{networks-of-control}
- <1-> Does the program let you disable those [anti-]features?
-
<2-> Pre-download location-sensitive data (e.g. street maps)
- <2-> OsmAnd (free software, Android and iOS)\cite{osmand}
So you may legitimately want GPS enabled. It's terrible that you should be concerned about it.
Are the programs you're using transparent in what they're sending? A precondition to that answer is source code.
A study by the Wall Street Journal found that 47 of the 100 Android and iOS apps in 2010 shared your location with not only the developers, but also with third parties.
An example is Angry Birds, which for whatever the hell reason was sending users' address books, locations, and device IDs to third parties.
You need to know what data you're leaking so that you can decide whether or not you want to do so. And you need the option to disable it. Or modify the program to disable it.
Sometimes your location is leaked as a side-effect. Navigation systems, for example, usually lazy-load map images. Some apps let you use pre-downloaded maps, like OsmAnd, which is free software available on both Android and—if you must—iOS.
Location Services
- <1-> No GPS? No problem!
- <1-> Mozilla Location Services, OpenMobileNetwork, … \cite{mozilla:loc-services,openmobilenetwork}
-
<1-> Wifi Positioning System; Bluetooth networks; nearby cell towers\cite{w:wps}
- <1-> Signal strength and SSIDs and MACs of Access Points \cite{w:trilateration,acm:spotfi,acm:lteye}
- <2-> Some gathered by Google Street View cars
- <2-> Your device may report back nearby networks to build a more comprehensive database
-
<3-> Works even where GPS and Cell signals cannot penetrate
- <3-> Can be more accurate than GPS (e.g. what store in a shopping mall)
But GPS doesn't need to be available. Have you ever used a program on a computer that asked for your location?
There are numerous services available to geolocate based on signal strength of nearby access points; bluetooth networks; and cell towers.
Some of these data are gathered by Google Street View cars. Devices that have GPS, like your phone might also be reporting back nearby networks in order to improve the quality of these databases.
Sometimes this can be more accurate than GPS. And it works where GPS and maybe even cell service don't, such as inside shopping malls.
So just because GPS is off does not mean your location is unknown.
Operating System [3/3]
Untrusted/Proprietary OS
-
<1-> Who does your phone work for?
- Apple? Google? Microsoft? Blackberry? Your manufacturer too?
- <1-> Carry everywhere you go, but fundamentally cannot trust it\cite{gnu:malware-mobile}
-
<2-> Some come with gratis surveillance
- <2-> BLU phones sent SMS messages, contacts, call history, IMEIs, and more to third-party servers without users' knowledge or censent \cite{kryptowire:adups}
A lot of this boils down to trust. Who does your phone work for?
Does your phone work for Apple? Google? Microsoft? Blackberry? Or does it work for you?
The OS situation on mobile is lousy. You carry around this computer everywhere you go. And you fundamentally cannot trust it.
Take BLU phones for example—cheap little phones that come with advertising. In November of last year it was discovered that these popular phones contained software that sent SMS messages, contact lists, call history, IMEIs, etc to third-party servers without users' knowledge or consent. That software could also remotely execute code on the device.
Free/Libre Mobile OS?
-
<1-> Android is supposedly free software
- <1-> But every phone requires proprietary drivers, or contains proprietary software
-
<2-> Replicant\cite{replicant}
- <2> Niche. Largely work of one developer now. (Help if you can!)

Android is supposedly a free operating system. Unfortunately, every phone requires proprietary drivers to work, and is loaded with proprietary software.
Does anyone here use Replicant? It is a fully free Android fork. I feel like I can at least trust my phone a little bit.
Modem Isolation
- But modem still runs non-free software\cite{replicant:sec}
- Sometimes has access to CPU, disk, and memory\cite{replicant:samsung-bd}
But on nearly every phone, the modem still runs proprietary software. And sometimes it has direct access to CPU, disk, and memory. Replicant closed a backdoor in Samsung Galaxy phones that allowed for remote access to the disk. That backdoor might not have been intentional, but it illustrates the possibility, and could still be exploited by an attacker.
So even with Replicant, I consider the device compromised; I put nothing important on it if I can avoid it.
Vehicles
Introduction B_fullframe
\Huge What about your car?
Okay, how about something else that's mobile: your car.
OnStar B_fullframe

\smallskip
∈cite{onstar:privacy-policy}
- Since 2011, retains all GPS and system data to sell to third parties
I vowed never to get a modern vehicle. Turns out, I can't afford the maintenance on older ones, and safety of my children is pretty important. I got a decent lease deal on a Chevy.
What have Chevys come with for the past 20 years? OnStar.
The first thing I did when I got home with the car was get out the manual, find that it had its own dedicated fuse, and pulled it.
How much could it possibly track? Well, here's the relevant portion of the OnStar privacy policy.
And since 2011, they retain GPS and system data to sell to third parties, presumably like insurers.
Ford B_fullframe

``We know everyone who breaks the law, we know when you're doing it. We have GPS in your car, so we know what you're doing. By the way, we don't supply that data to anyone.''\cite{binsider:ford-gps}
\hfill—Jim Farley, VP/Marketing and Sales, 2014
And then you have stupid executives saying crap like this:
<Read quote>
Oh, excellent! I'm assured.
It's a problem that VPs don't think this is a problem and will just say it off the cuff.
Stationary [5/5]
Introduction [0/1] B_ignoreheading
Introduction B_fullframe
\large ``If you've got nothing to hide, you've got nothing to fear.''\cite{rosen:naked,solove:nothing-to-hide,metro:goebbels}
\hfill—Joeseph Gobbels, Nazi propaganda minister
\hfill—Richard Graham, British MP
Well, speaking of stupid quotes!
So let's say you have evaded that type of tracking. Maybe you don't carry a phone, or drive a car instead of a computer.
This quote. It's by a Nazi minister for Enlightenment and Propaganda. It's also by the British member of paralement defending a British surveillance program.
There's certain things that are nearly impossible to avoid.
Surveillance Cameras (CCTV) [4/4]
Private Cameras in Plain View; Tinderloin, SF
 ∈cite{cbs:sf-smile}
∈cite{cbs:sf-smile}
``The idea that you can sort of meet in a public place and quietly have a conversation that we’re sort of accustomed to from spy movies, that is really not realistic anymore,'' —Nadia Kayyali, EFF\cite{cbs:sf-smile}
This is a map of private surveillance cameras in plain view around a San Francisco neighborhood. And these are just the ones that the DA's office found in plain view!
According to them, people who live in this neighborhood could be on camera dozens of times in a single day.
Alright, so a bunch of private entities have you on camera; So what?
Access to Data
- <1-> Data can be obtained with a warrant or subpoena
- <2-> Data can be compromised
- <3-> Chilling effect
-
<4-> If you own a surveillance system, be responsible and considerate
- <4-> Best way to restrict data is to avoid collecting it to begin with
Well one of the most obvious threats, should it pertain to you, is a warrant or subpoena.
Most of us aren't going to have to worry about a crime. But data can be compromised. And it isn't possible for you to audit it; you have no idea who has you on camera.
This creates a chilling effect. You're going to act differently in public knowing that someone might be watching, or could be watching later on if recorded.
If you have a surveillance system, or any sort of public-facing cameras, please be considerate. If you only care who is on your property, don't record the sidewalk in front of your house. Or at least restrict motion detection to your property. The best form of privacy is to avoid having the data be collected to begin with.
Domain Awareness System (Intro) B_fullframe
\only<1>{What if all those cameras—including private—were connected?} \only<2>{\Huge NYPD\par Domain Awareness System∈cite{nyc:pspg}} \only<3>{
\large Although NYPD documents indicate that the system is specifically designed for anti-terrorism operations, any incidental data it collects ``for a legitimate law enforcement or public safety purpose'' by DAS can be utilized by the police department.\cite{fast:das}
…but what if law enforcement didn't have to go door-to-door?
Let's talk about the NYPD's Domain Awareness System. That quote from the British MP and Nazi guy— it was in reference to the system that served as the basis for this one.
It was designed in part for supposed terrorism threats after 9/11. But any data this system collects for ``legtimate'' law enforcement or public safety purposes can be used against you.
You may not know this, though, because they may not want to bring this evidence to court. There's a disgraceful practice of ``parallel construction'', where law enforcement will instead—after having found whether a person is, say, guilty of a crime—go find other unrelated evidence to prove it.
Domain Awareness System
-
<1-> Partnership between the NYPD and Microsoft at a cost of $230M in 2013\cite{reuters:nypd-das,nyc:pspg}
- <1-> Surveillance cameras, license plate readers, radiation detectors, 911 system, criminal records, \ldots
- <1-> > 6,000 surveillance cameras, $2\over 3$ private businesses\cite{reuters:nypd-das,pbs:nova:boston}
- <2-> Database of over 16 million plates, every car going into Lower Manhatten\cite{reuters:nypd-das,pbs:nova:boston}
- <3-> Can search in seconds for terms like ``red baseball cap''\cite{reuters:nypd-das,pbs:nova:boston}
- <3-> Detects ``suspicious behaviors'' like unattended bags and circling cars\cite{reuters:nypd-das,pbs:nova:boston}
The Domain Awareness System is a partnership between Microsoft and the NYPD. It's mammoth.
It contains over six thousand security cameras, over two-thirds of which are private closed-circuit cameras. It includes license plate readers that record everyone going into Lower Manhattan, along with a database of over sixteen million license plates. It can search in seconds for very specific terms, like ``red baseball cap'', and it can monitor for suspicious behaviors, like unattended bags, or cars circling an area. If it finds an unattended bag, you can rewind to find who left it.
This is the direction we're heading in— these things will only spread. In fact, the NYPD will get a 30% cut when Microsoft sells it to others.
Driver Surveillance [3/3]
Automated License Plate Readers (ALPRs)
Images
 \par∈cite{eff:alpr}
\par∈cite{eff:alpr}
 \par∈cite{eff:alpr}
\par∈cite{eff:alpr}
 \par∈cite{aclu:tracked}
\par∈cite{aclu:tracked}
Summary
- Scan passing cars' license plates\cite{aclu:tracked,eff:alpr}
- Produce alphanumeric representation with timestamp and photograph
I want to talk about a couple issues related to driver surveillance. These things are a widespread, nasty threat to privacy, and they don't need a sophisticated Domain Awareness System to deploy.
The first are ALPRs. ALPRs are mounted on police cars and objects like light poles. They scan passing cars' license plates, convert them to alphanumeric data, record the time and date, and possibly an image of the vehcile. Here's a screenshot of the interface of one; we'll get into how exactly we got that in a bit. The ACLU has an excellent report on it, and the EFF has a campaign against it; see those two resources for more info.
Automatic Toll Readers
-
<1-> Electronic toll booth using RFIDs or ALPRs\cite{eff:golden-gate-toll}
- <1-> In the North-East we have E-ZPass (RFID)\cite{w:ezpass}
- <1-> Golden Gate Bridge requires FasTrack or plate-based
- <2-> But they provide an option for an anonymous FasTrack account using cash\cite{goldengate:anon}
- <2-> (Granted, you're still captured by an ALPR)
- <3-> Routinely used by law enforcement\cite{baynews:fastack-data}
- <3-> …and divorce cases, in case of FasTrack
- <4-> They're not very secure—easily cloned either\cite{blackhat:toll-systems,register:rfid-clone}
Electronic toll booths are replacing traditional cash-based tolls. Some places require it, like the Golden Gate Bridge. Windshild-mounted RFIDs or ALPRS. In the North-East, we have E-ZPass. For the Golden Gate Bridge, FasTrack.
We've already seen that law enforcement uses these data, but in the case of FasTrack, data are even used in civil suits like divorces.
And they have their security issues; many can be easily cloned, for example.
Akin To GPS Tracking
- United States v. Jones: GPS tracking constitutes search under Fourth Amendment\cite{w:us-v-jones}
- How is pervasive surveillance different if it achieves essentially the same result?
In the US Supreme Court case United States v. Jones, the judges unanimously ruled that GPS tracking of a vehicle constitutes a search under the Fourth Amendment.
Many wonder how tracking as I just described is any different. If you have ALPRs and other surveillance systems throughout the same area within which a warrant for GPS tracking can be executed, you would get similar results. With much less risk, too—no secret device that may be discovered.
That's for a court to eventually decide.
Internet of Things [13/13]
Internet-Connected Cameras B_fullframe
\Huge
In the past, these cameras were on their own segregated networks. You'd have to subpoena the owner or get a warrant, or otherwise physically take the tape.
Today…that might be the intent, but these cameras are often connected to the Internet for one reason or another. It might be intentional—to view the camera remotely or on a device—or it may just be how the camera is set up by default.
Well… It's not just businesses that use Internet-connected cameras. They're also popular among individuals for personal/home use so that they can view them on their smart phones and elsewhere. Like home security systems. Baby monitors.
The ``S'' In IoT Stands For ``Security''
-
<1-> Shodan—IoT search engine\cite{shodan}
- <1-> You'll also find other things. Secure your databases. \cite{krebs:mongodb}
- <1-> Can search for specific devices
-
<1-> If you are vulnerable, someone will find you
- <1-> Mirai—620Gbps DDoS Krebs; 1Tbps OVH
Who here has heard of Shodan?
Shodan is a search engine for the Internet of Things. It scours for Internet-connected devices and indexes them. Maybe it wouldn't be a problem if these devices even gave a moment of thought to security.
It also indexes other interesting things. For example, it was used to find unsecured MongoDB instances so that the attackers could hold data for ransom.
Mirai is malware that took advantage of default usernames and passwords for over 60 devices to create a massive botnet that carried out the largest DDoS attacks in history.
Who's Watching?
Screenshot
 \par∈cite{insecam}
\par∈cite{insecam}
Summary
- Insecam is a directory of Internet-connected surveillance cameras\cite{insecam}
- Live video feeds (browser connects directly to cameras)
What about Insecam?
It's a site that aggregates live video feeds of unsecured IP cameras. Your browser connects directly to the cameras— literally, they are wide open; nothing fancy is going on here. I can tell you personally that you feel like a scumbag looking at the site.
Insecam Example 1 B_fullframe



Here are some examples. I blurred any identifying features for privacy.
We have surveillance rooms where people watch their surveillance system! Inception-kinda thing going on here. Also doesn't help that they are watching the TV on the wall too.
There's many public swimming pools.
Elevators are awkward enough to begin with. How about someone watching you in such a vulnerable space?
We have a photolithography lab in my home city. I have no idea which one, or where exactly.
These are creepy. Somewhat cool, even. Let's get a little more personal.
Example 2 B_fullframe


How about inside hospital rooms? This patient has an ice pack strapped to the side of her face. I'm pretty sure this feed was outside of the United States; I can't imagine that this type of thing would make it past HIPAA audits.
How about inside someone's home? This looks to be a bedroom. There is a family photo on the wall. Oh yeah.
I saw someone at the dentist getting a teeth cleaning. I didn't copy that photo at the time, and I can't find it now, fortunately.
This is an excellent example to demonstrate to others why this is such a big deal. This should make anyone feel uncomfortable.
These people are unaware. And these manufactuers set them up for this.
Smart TVs (Samsung Privacy Policy) B_fullframe
``Please be aware that if your spoken words include personal or other sensitive information, that information will be among the data captured and transmitted to a third party through your use of Voice Recognition.''
\hfill—Samsung SmartTV Privacy Policy, 2015
\cite{eff:samsung-tv-policy}
So while we're on the topic of being in someone's home…
Samsung's SmartTV privacy policy caused a big fuss a couple years ago by blatantly stating that your personal conversations will be sent to third-party servers for voice recognition.
It was compared to George Orwell's telescreens.
<Read above>
Smart TVs (Weeping Angel) B_fullframe
Wikileaks

Title
\par∈cite{vault7:weeping,vault7:y0}
- Suppress LEDs for ``fake off''
- Record audio
- Remote shell and file transfer
- Extract WiFi credentials
- ``TODO'': Record video
But it might not be Samsung that's listening.
Recently, Wikileaks released what it refers to as ``Vault 7'', an unprecedented doxxing of the CIA.
Weeping Angel was one of the projects. It targets Samsung Smart TVs and can suppress LEDs to enter what they call a ``fake off'' mode, covertly listening to the environment. As of their 2014 notes, video surveillance was explicitly on their TODO list. I find it unlikely that they didn't succeed given that they appear to have root access to the device.
CIA

If Samsung isn't listening, then others might be.
Smart TV Ransomware (LG)

∈cite{bleep:lgtv-ransom}
Remember: if the CIA exploited a vulnerability, it's very possible that other adversaires have as well; it isn't just the CIA you have to worry about.
This is an LG Smart TV owned by Android ransomware.
Vulnerabilties Equities Process (VEP)
- Whether or not government should disclose vulnerability
- Hoarding is dangerous (Shadow Brokers / Equation Group; Vault 7 / CIA)
- Apple v. FBI
-
<2> Makes us less safe!
- <2> ``Cyberweapon'' is an exploit—it cannot be contained
Amazon Echo—Always Listening
Echo echo echo echo…

∈cite{w:file:echo}
Summary
- Voice recognition on Amazon's servers; have recordings \cite{engadget:murder-echo,guardian:murder-echo}
- Warrant issued in murder case for recordings \cite{engadget:murder-echo,guardian:murder-echo}
-
Always listening; ``wake word'' doesn't matter (they control the software; device can be compromised)\cite{gizmodo:echo-wiretap}
- <2-> Should do voice recognition on the device
- <2-> Run free software
- <2-> Connect to your own server for actions
- <2-> Hardware switch for microphone
Amazon Echo is one of those ``always-listening'' devices that can do your bidding. But since it performs voice recognition on Amazon's servers, they have access to recordings of your data. A court has issued a warrant for those recordings in a murder case in December of this past year.
Look: a device like this—one that is always listening— is a security nightmare. It doesn't matter if it has some sort of ``wake word''; functionality can be hidden from you or changed with an update. You do not have control over that device or the software that it is running. If an attacker owns the device, they're sitting there in your living room. A device like this needs to do voice recognition locally, run free software, connect to a server of your choosing for actions. and have a hardware switch for the microphone.
Consder the Benign
-
Water meter used in murder case as evidence\cite{guardian:murder-echo}
- 140 gallons between 1AM and 3AM in Winter?
-
Thermostat?
- Usage patterns could hint at when you're home
- Window/door sensors?
Consider what devices in your home might have access to.
That murder case I just mentioned with the Echo— they also gathered data from the water meter which showed that the suspect used 140 gallons between 1AM and 3AM. During Winter, nonetheless.
Your thermostat could reveal usage patterns to determine remotely when you might be home. There are door and window sensors.
Creepy-Ass Children's Toys?
 ???
???
 ∈cite{guardian:doll-spy}
∈cite{guardian:doll-spy}
What about creepy-ass children's toys? I took a screenshot of this Guardian article because… A couple years ago you'd only find a headline like this in something like The Onion.
``German watchdog classifies My Friend Cayla doll as `illegal espionage apparatus'.''
What the hell.
ALPRs Wide Open
 ∈cite{eff:alpr}
∈cite{eff:alpr}
- John Matherly (Shodan author) noticed many web-accessible PIPS control panels
- Other researcher found some accessible via telnet\cite{darius:alpr-telnet}
Alright, well, stupid things happen outside the home too. Those ALPRs we just talked about.
Turns out that they have web interfaces. John Matherly, the author of Shodon, found a number of control panels for PIPS ALPRs. Another researcher found telnet access on some. In both cases, license plate data could be extracted, and the system could be reconfigured.
Biometrics
- <1-> Humans no longer need to scour video feeds\cite{eff:facial-tech,churchix,facefirst,pbs:nova:boston}
-
<1-> Facial recognition widely used, even for mobile apps\cite{register:fb-scan,eff:ios-photo-diff,eff:fbi-bio}
- <2-> NYPD has a gallery of over 4M individuals\cite{pbs:nova:boston}
- <2-> Quality can be low and pixelated; various machine learning algorithms\cite{pbs:nova:boston,wired:pixel-face,arxiv:google-pixel-res}
- <3-> No face? Check your gait.\cite{ieee:gait,ijca:gait}
- <4-> No gait? Well\ldots whatever, just ask Facebook.\cite{newsci:fb-noface}
- <5-> Even fingerprints and iris from high-resolutions photos (defeat Apple's TouchID)\cite{bio:iris}
Now let's couple that with facial recognition.
Consider the breadth of devices we just covered. People don't need to manually look for you anymore; it's automated. Hell, any of us can download a free (as in freedom) library to do facial recognition and train it to recognize people. It doesn't even have to be clear— there's machine learning algorithms to reconstruct pixelated faces with somewhat decent accuracy to be useful. The NYPD has over 4 million people's images in a database that they compare against during facial recognition.
Don't have a face? You can also be identified by your gait. No gait? Facebook famously got even creepier by saying it could recognize people by their dress, posture, and hair, without even seeing their face.
Your fingerprints and iris data can even be extracted from high-resolution photos; a cracker used such a method to defeat Apple's TouchID by making a mould.
Social Media [1/1]
Collateral Damage
- <1-> Please don't put pictures of me on Facebook\cite{rms:facebook}
- <1-> Don't put pictures of my children _anywhere_\cite{techcrunch:fb-baby}
- <2-> That person in the distance is collateral damage\cite{register:fb-scan,guardian:fb-scan,pbs:nova:boston}
You also have unsecured people running wild with their photos and their selfies.
I'm sure you've heard a frequent request/demand from rms: "Don't put pictures of me on Facebook." It's excellent surveillance. What irks me is when people try to take pictures of my kids, or do and ask if they can put them online. And people are sometimes surprised by that refusal.
Most people are being innocent— they're just trying to capture the moment. What they're actually doing is inflicting collateral damage. If I'm off in the background when you take a picture of your friends in the foreground, I'm still in the photo.
The Web [7/7]
Introduction [1/1] B_ignoreheading
Introduction B_fullframe
\Huge Fleshy You $\Longleftrightarrow$ Virtual You
But you're not just tracked in the flesh. Much of what we do today is virtual. So, naturally, there are those that want to bridge them.
Bridging the Gap [3/3]
FTC: They're Watching You B_fullframe
 \par∈cite{ftc:silver}
\par∈cite{ftc:silver}
This is a sample letter template from the FTC. A challenge for advertisers is correlating users across multiple devices, and in the real world.
Sometimes commercials have you enter promo codes, or give you a unique URL.
Ultrasound Tracking
⋯ $\Longleftrightarrow$ TV $\Longleftrightarrow$ Retail Store $\Longleftrightarrow$ Mobile $\Longleftrightarrow$ Web $\Longleftrightarrow$ ⋯
-
Correlates users across devices; airgap bridge\cite{ubeacsec:paper,wired:ultrasonic}
- Inaudible to humans
- Could deanonymize (e.g. Tor users)\cite{33c3:talk-behind,bleep:ultrasound-tor}

``Silverpush could generate a detailed log of the television content viewed while a user’s mobile phone was turned on.''\cite{ftc:silver}
Others play inaudible sounds that are picked up by your mobile device or computer.
This has other serious implications. There are concerns, for example, about this method being able to be used to deanonymize Tor users.
In that letter, FTC mentions Silverpush by name. There are other companies too; see the references.
Ultrasound Cross-Device Tracking (uXDT)
- <1-> Termed ``Ultrasound Cross-Device Tracking'' (uXDT)\cite{bleep:ultrasound-tor,ftc:xdt}
-
<1-> Mitigations?
- <2-> SilverDog is a Chromium addon to filter HTML5 audio\cite{ubeacsec:paper}
- <3-> Don't install software that keep secrets (proprietary)
- <3-> Don't run untrusted code on websites (use e.g. NoScript)\cite{mtg:rof}
- <4-> Turn off your device when not in use
- <4-> Keep device away from other media
This is termed ``Ultrasound Cross-Device Tracking'', or simply ``Cross-Device Tracking''. How do you go about mitigating this type of threat?
Well, researchers studying this issue wrote SilverDog, a Chromium addon to filter HTML5 audio to remove ultrasonic frequencies. That doesn't help with TorBrowser, though, which is FF-based.
This type of thing only works when you're keeping some serious secrets. That's easy to do with proprietary software. Much riskier to do (but not impossible) with free software. For websites, don't run untrusted JavaScript code; block it with an addon like NoScript.
You can also turn off the device when not in use, and maybe keep it away from other media.
Analytics [4/4]
Introduction B_fullframe
\only<1-3>{ {\Huge Data Analytics}
\uncover<2-3>{\LARGE (Building User Profiles)}
\uncover<3>{\large (Tracking)} }
\only<4->{ {\Huge Spyware}
\uncover<5>{\LARGE (With Science)} }
This all leads into a larger subject called ``data analytics''.
Which is really just building, analyzing, and aggregating user profiles.
Which is generally called tracking.
…which we usually just call spyware. But this has science!
Trackers
-
Website owners want to know what their visitors are doing
- That in itself isn't an unreasonable concept
- Methods and data define the issue
Website owners want to know what their visitors are doing. That in itself isn't an unreasonable thing, broadly speaking, but how you go about it and what types of data you collect defines the issue.
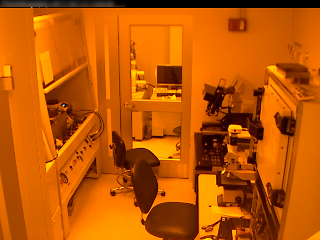
Google Analytics
GA Dashboard

∈cite{google:ga:features}
 ∈cite{w3techs:analytics}
∈cite{w3techs:analytics}
Description
- <1-> User location, screen resolution, time on page, heatmap, etc\cite{w:behavioral-targeting}
- <1-> Unique identifier assigned
- <1-> Fine-grained reporting for site owner
- <2-> Knows many sites user visited across Web\cite{w3techs:google}
Take Google Analytics for example. It is one of the most widely distributed spyware programs in the world.
It collects a variety of user data. A lot of it really is what website owners want to know: geography, screen resolution, time on the page, heatmaps, etc. Except…
All of this is known to Google. And because services like GA, AdWords, etc are so widely used, all of this can be used to identify users across the entire web.
Piwik
Dashboard

∈cite{piwik}
Description
- Data on **your own servers**\cite{mtg:gitlab-piwik}
- Visitor privacy settings\cite{piwik:privacy}
- Privacy as a site owner
If you must track your users, consider using Piwik, which you can host yourself. This means that your visitor data aren't stored and accessible by Google or other companies. Pwik has some user privacy settings to anonymize, remove logs, respect DNT, provide opt-out, etc. It also gives website owners some privacy by not leaking paths and other information about the website:
I shout out to GitLab—I suggested that they replace GA with Piwik on their instance, and they did with no resistence.
Social Networking
Like Buttons
 ∈cite{w:fb-like-img}
∈cite{w:fb-like-img}
- Infecting the Web with trackers under guise of community\cite{pnas:predict,w:behavioral-targeting,uld:fb}
- Tracks regardless of whether you are logged in to Facebook \cite{bloomberg:belgum-fb,roosendaal:fb-like,networks-of-control}
Another popular example are "like buttons" and similar little widgets that websites like Facebook offer. It might help get the word out about your stuff, but please don't fall into the trap of betraying your visitors. Please don't fall into the trap of clicking it, either— it's easy to infer a great deal of information about you from what you "like".
If a user is logged into Facebook, then Facebook now knows that they visited that website, even if they don't click on the button.
But even if you don't have a Facebook account, you are still being tracked.
Fingerprinting [3/3]
Summary B_fullframe
\Huge Fingerprinting
These methods are part of a broader topic called ``fingerprinting''. It's just what it sounds like: uniquely identify users online and across devices and such.
EFF Research B_fullframe
EFF Research, 2010:\cite{eff:browser-uniqueness-blog,eff:browser-uniqueness}
``In our analysis of anonymized data from around half a million distinct browsers, 84% had unique configurations. Among browsers that had Flash or Java installed, 94% were unique, and only 1% had fingerprints that were seen more than twice.''
That was seven years ago.
You're really screwed today.*
∈cite{eff:panopti2,eff:browser-uniqueness,mozilla:fingerprinting,% chromium:identification,tor:browser-design,stanford:private-browsing,% norte:tor-fingerprint,browserleaks,ars:fingerprint,hardware-fingerprint}
Back in 2010, the EFF released a paper with results from their fingerprinting research project Panopticlick. Back then, they had an 84% success rate; even higher with Flash and Java.
But we ain't in 2010 anymore. We have options. Very creative ones.
Alarmingly Effective
- Panopticlick (EFF)\cite{panopti:about}
- User Agent, cookies, screen resolution, fonts, language, session storage, canvas, WebGL, ad blocker, audio, keystrokes, mouse movement, \ldots\cite{ijcseit:biometric}
- Can even track separate browsers on the same hardware\cite{hardware-fingerprint,ars:fingerprint}
Fingerprinting is alarmingly effective. We don't have time to get into much detail on how it works; I provided plenty of resources for that. But there are some interesting ones.
How about tracking how the user moves her mouse and scrolls? What about keystroke analysis? Random noise from audio? Time of CPU-intensive tasks like rendering 3D elements?
Some of these methods are hardware-based. They can fingerprint even if the user opens a different browser, or maybe even a different operating system, on the same box.
Some are behavioral. Keystroke patterns will persist wherever the user goes.
Incentive to Betray [2/2]
How Does This Happen?
-
There is strong incentive to betray
- Money (advertising)
- Attention & praise
- ``Business intelligence''
So how does tracking happen? How does this tracking code get on so much of the web?
Incentives to betray users.
Many websites make money through advertising. It can be lucrative. And it's easy to do.
Others get addicted to attention and praise.
Others simply want to know what their visitors are doing on their website.
Most website owners don't think or know about these issues. They're unknowing pawns in the Web of surveillance.
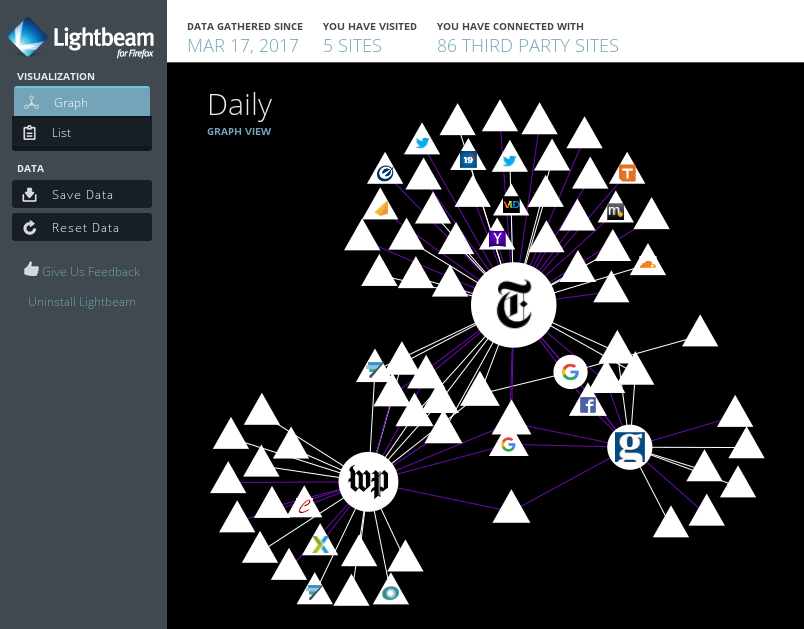
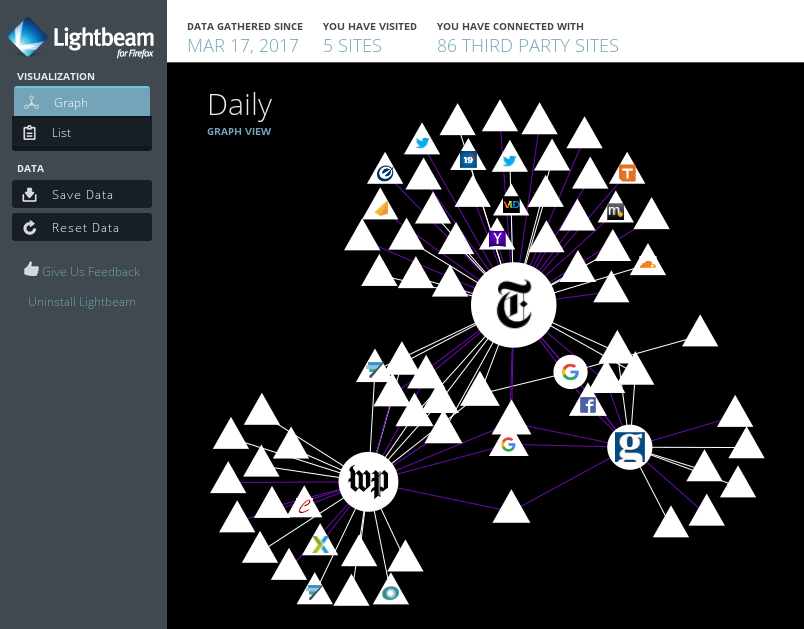
Web of Surveillance B_fullframe
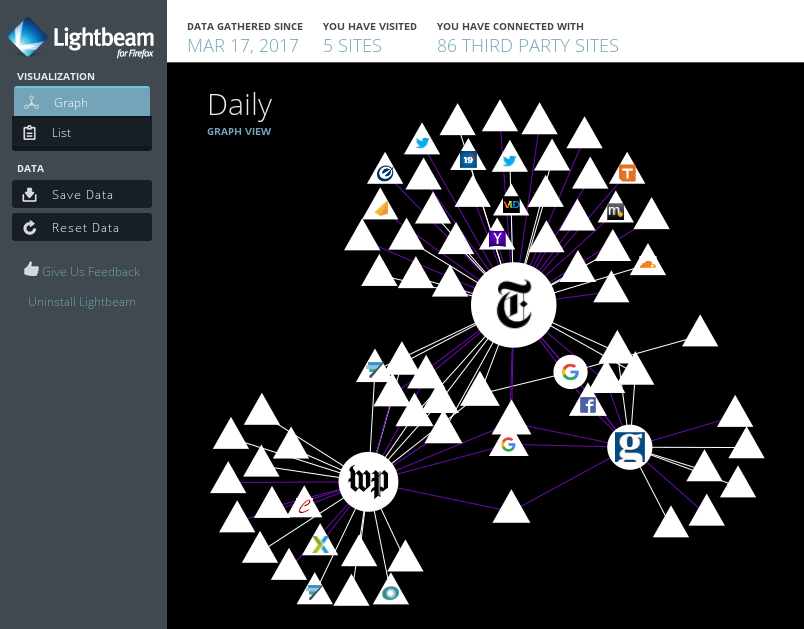
∈cite{moz:lightbeam}
(After mitigations)
And I do mean a Web of surveillance.
This is LightBeam. It's an addon for Firefox that graphs first- and third-party sites that you visit. I created a new FF profile and installed the addon; none of my privacy settings or other addons I'm used to. You can see at the top that I visited five websites: Washington Post, NY Times from Google, Guardian, and—which you can't see here because they're actually disjoint from this graph—The Intercept. Good for them! And yet, it hit 86 third party sites! NYT alone connected to 47 different third parties!
I was blown away.
So let me show you what I'm used to seeing. This is what happens when I try to mitigate some of these threats.
Mitigations & Anonymity [8/8]
Summary B_fullframe
\Huge How Do We Mitigate?
So how do we do that?
Well, it depends on your threat model, but let's start with the easy stuff.
Disable the Damn JavaScript!

-
Preempt most sophisticated and damning fingerprinting methods
- Stop hardware profiling
- Stop keystroke/mouse analysis\cite{ijcseit:biometric}
- Remember those audio beacons?\cite{bleep:ultrasound-tor}
-
Running arbitrary untrusted, unsigned, ephemeral code (also from many third parties)\cite{mtg:rof}
- Restore Online Freedom! (My LibrePlanet 2016 talk)
- LibreJS blocks non-free, but free doesn't mean free of malice
-
NoScript blocks JavaScript based on URL patterns\cite{noscript}
- Warning: Allows some sites by default!
- Also blocks media and fonts; provides XSS and clickjacking prevention
Okay, I can't say this enough. Disable the damn JavaScript! The Web isn't broken without it, they're breaking the web with it! I write a lot of JavaScript for a living. My GNU project is ease.js, which is a JavaScript library. And yet, I only allow JavaScript to execute on a few websites!. You're runnning untrusted, unsigned, ephemeral code, often from many third parties! But I've already given that talk— see Restore Online Freedom! from last year!
Some people run LibreJS, and I support that project. But note that free software doesn't mean free of malice; LibreJS solves a different problem than the one I'm describing— when you do allow JS to run, ought to be free.
It's probably obvious from the logo that I'm talking about the NoScript addon. It does more than just block JS— it also blocks certain types of attacks.
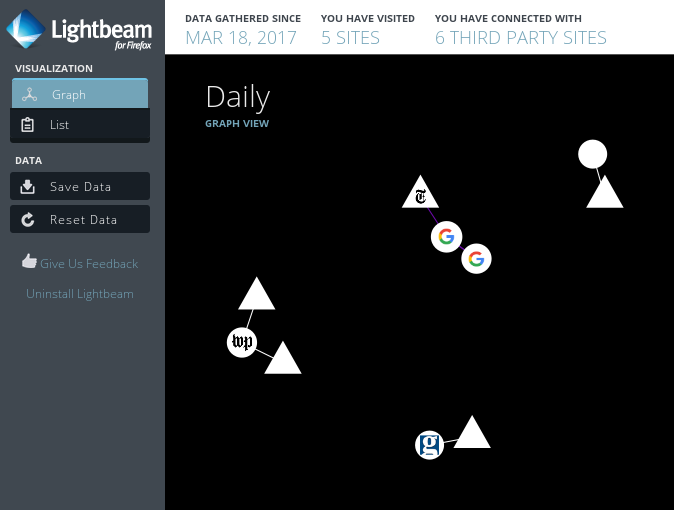
LightBeam NoScript B_fullframe
(Before NoScript)
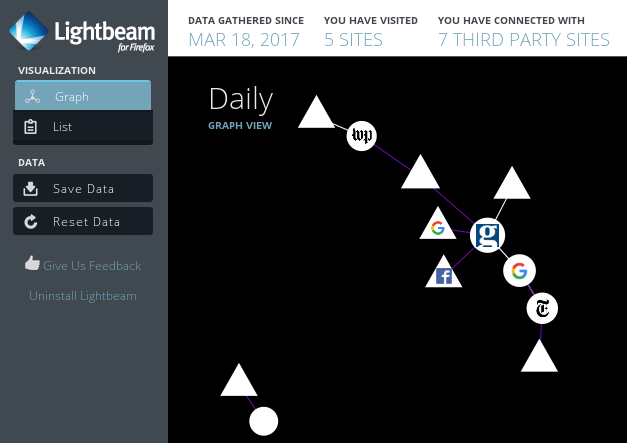
(After NoScript with no whitelist)
So this is our graph again before NoScript.
And here it is after running NoScript with no whitelist. Without any other mitigations.
Obviously results will vary depending on the website.
Ads/Trackers; Security



- Privacy Badger blocks trackers\cite{eff:privacy-badger,lp:2016:privacy-badger}
- uBlock_0 ``wide-spectrum blocker''\cite{gh:ublock-origin}
- Self-Destructing Cookies clears cookies and LocalStorage\cite{moz:sd-cookies}
The issue surrounding Ad Blockers is framed such that we're waging war against advertisers. No—they're waging war against us.
You'll find that the bulk of what these addons handle is related to ad networks. Privacy Badger works to block sites that appear to be tracking you. Cooper Quintin—developer of Privacy Badger—gave a great talk last year here at LP; go check it out. uBlock Origin describes itself as a ``wide-spectrum blocker'', but it serves primarily as an ad blocker. Self-Destructing cookies clears out a site's cookies and LocalStorage once a tab is closed. There may be better options out there; this seems to be useful for me.
I don't have time to go into technical details, unfortunately.
HTTPS Everywhere B_fullframe

Anonymity B_fullframe
\bigskip Origin is unknown to server; unique identifier is available to server∈cite{whonix:donot}
\bigskip Origin is unknown to server; no unique identifier known by server∈cite{whonix:donot}
Another way is to be anonymous or pseudononymous. In the latter case, you assume a pseudoynm online and perform only activities that should be associated with that pseudonym. In the former case, there should be no way to ever correlate past or future actions with your current session.
IANAAE B_fullframe
(I Am Not An Anonymity Expert)
This is a difficult topic that's pretty dangerous to give advice on if you have strong need for anonymity—for example, if you are a dissident or whistleblower. If your life depends on anonymity, please do your own research. I provide a number of resources to get you started.
The Tor Network

 ∈cite{tor:overview}
∈cite{tor:overview}
- <1> The Onion Router (Tor)\cite{tor}
- <1> Helps defend against traffic analysis
Most here have probably heard of Tor. Its purpose is to protect against certain kinds of traffic analysis.
"Tor" stands for "The Onion Router", which describes how it relays data through the Tor network.
The packet is routed through a number of servers, encrypted with the public key of each server such that the first hop strips off the first layer and so on, like an onion.
Barring certain very important technical details, it should not be possible to figure out that path.
There are caveats. Please do your research.
TorBrowser, Tails, and Whonix



- Also need to change browsing habits\cite{whonix:donot}
-
Browser needs to be hardened
- Remember: browser leaks a lot of data\cite{panopti:about,eff:browser-uniqueness}
- TorBrowser is a hardened Firefox derivative\cite{tor:browser,tor:browser-design}
-
<3-> Operating System needs to be hardened
- <3-> Tails—The Amnesic Incognito Live System\cite{tor:tails}
- <4> Whonix—Multi-layer isolation in VMs\cite{whonix}
But Tor alone isn't enough to secure your anonymity. You also have to change your browsing habits. That is difficult and nuanced advice to give, let alone in a mention in a talk, so I defer to my citations.
For some people, that's enough. If your threat model involves only advertisers and other snoopers, you might be okay with Tor and privacy extensions.
But if you're a dissident, and your life is in danger, you have more work to do. If you are worried about government surveillance or cracking, you have more work to do.
It's hard to secure a web browser.
TorBrowser is a hardened version of Firefox. The Tor Project recommends that you don't rely on a vanilla Firefox for anonymity with Tor.
The operating system needs hardening. There are two major options. The first one is Tails: The Amnesic Incognito Live System. It is an ephemeral OS that you can simply boot from USB on any PC. It routes all traffic through the Tor network.
The second is Whonix. It is not ephemeral: it requires a host OS (or hypervisor) and runs two VMs: one is the guest that the user uses as a desktop, and the other is the VM it routes all traffic through, which goes through Tor. If the guest the user is using is compromised, an attacker cannot subvert the Tor network.
There's obvious tradeoffs there for both; I encourage you to look into both before deciding which is best for your threat model.
Data and Profiling [4/4]
Introduction B_ignoreheading
Introduction B_fullframe
\Huge ``Big Data''
(Your Big Data)
\Huge ``Business Intelligence''
We've seen adversaries with different motives. Let's explore what some of them do with all those data.
This is a ``big data'' problem. You might also hear this called ``business intelligence''.
Those Who Spy
Data Brokers
Lightbeam Reminder
Summary
- Ghostery lists *over 3,000 companies receiving web/app data*\cite{ghostery:companies}
Back to that Lightbeam graph of third parties. Ghostery has a list of third parties receiving web and app data. There's over 3,000 of them.
Oracle Identity Graph

\footnotesize ``Aggregates and provides insights on over $2 trillion in consumer spending from 1,500 data partners across 110 million US households''\cite{oracle:datalogix-acq}
Look how happy she is to be tracked! I'm kidding of course. If we put some random person's picture in her place, they might feel a bit uncomfortable.
Alright, Oracle Identity Graph. <Read quote>
Look at that last bullet point there. ``Deliver a more relevant customer experience''.
All About the Experience B_fullframe
\Huge ``More Relevant Customer Experience''
More relevant customer experience. You hear that a lot from advertisers, especially for justification.
Target Pregnancy Prediction

- Records purchases, credit cards, coupons, surveys, refunds, customer helpline calls, email, website visits, \ldots\cite{networks-of-control}
- Purchase more information from third parties\cite{networks-of-control}
-
Identified 25 products to create a ``pregnancy prediction'' score and estimate due date\cite{nyt:learn-secrets}
- Quantities of types of lotions, soaps, cotton balls, supplements, etc
One of the most popular examples of these types of analytics is a case where a father received coupons for baby clothes in the mail for his daughter. Target successfully predicted that she was pregnant based on certain items that she purchased, like quantities of certain lotions, and even things like cotton balls. They call this a ``pregnancy prediction''. It's creepy. It's lucrative.
Transparency Needed
Trustev Graph

∈cite{trustev:tech}
Summary
- Let users see their data in this graph!
- Erase nonpublic information that they don't want to be known
-
Let them correct what is wrong
- Also a problem with law enforcement / government
- Let them opt out!
Look, at the end of the day, some people do legitimately want this. They want to have this ``relevant customer experience''.
What we need is transparency.
Companies like Oracle should let you see your data in this graph. Let you correct it if it's wrong. Erase it if it's nonpublic information that you don't want to be known. And allow you to opt out!
We talked about government surveillance a while ago. This is a problem there as well. What if you're flagged as suspicious? Put on some no-fly list or terrorism watch list? What if it were based on completely wrong information inferred by some algorithm?
Let's look at that graph on the left a little more closely.
These Data Affect Your Life!
Trustev Fraud Detection

∈cite{trustev:tech}
This is a graph of sources for TransUnion's fraud prevention system. There are a lot of data sources here. And look at the node at the bottom— ``machine learning''.
What if this were wrong? You'd be flagged as a fraud. This could be inconvenient— like not being able to make an online purchase. But what if you are denied a loan because of things like this? Or…denied employment?
LexisNexis

- Risk management for insurance, finance, retail, travel, government, gaming, and healthcare\cite{networks-of-control}
- Data on over 500 million customers
- TrueID—34 billion records from over 10,000 sources\cite{lexisnexis:trueid}
``We help insurers assess their risk and streamline the underwriting process in 99% of all U.S. auto insurance claims and more than 90% of all homeowner claims.''
There's a ton of these companies; we only have time for a few. LexisNexis is another popular one. And it's fun to say.
They handle risk management for various industries, including government. And they pull from a pool of data of over 500 million customers.
<read quote>
To give you an idea of their scale: they also have a system called TrueID, which does identity verification for fraud detection. They aggregate tens of billions of records from over ten thousand sources.
Palantir

- Started by Peter Thiel of PayPal
- CIA, DHS, NSA, FBI, the CDC, the Marine Corps, the Air Force, Special Operations Command, West Point, the Joint IED-defeat organization and Allies, the Recovery Accountability and Transparency Board and the National Center for Missing and Exploited Children.\cite{techcrunch:palantir}
Another highly controversial one is Palantir. It was started by one of the co-founders of PayPal, Peter Thiel, for terrorism intelligence. It's now used for its powerful analytic capabilities by not only private corporations, but numerous three-letter government agencies.
Yeah. What if these data are wrong?
More Information
Networks of Control B_fullframe

∈cite{networks-of-control,33c3:surveil}
Shock and Awe
If this topic interests you, you need to read the paper Networks of Control. One of the authors gave a talk at the recent Chaos Communication Congress, and I was in both shock and awe. I've only had the chance to skim the paper. Both are referenced here.
Policy and Action [0/6]
Introduction [0/1] B_ignoreheading
Introduction B_fullframe
\Huge We're feeding into all of this!
SaaSS
Software as a Service Substitute (SaaSS)
- Disturbing trend to replace traditional software with services
- Do not own your own data or computations
-
Companies balance privacy on their balance sheets
- Countless data breaches
Centralization
Decentralize!
- Host what you can (GNU Social, NextCloud, \ldots)
- Damnit, Moxie (Signal)—use XMPP, OMEMO
People Don't Care
``I Have Nothing To Hide'' B_fullframe
\Huge ``I Have Nothing To Hide''
People don't care about privacy!
Complacency
\Huge Complacency in the Status Quo
Your Fight
Status Quo Cannot Hold B_fullframe
\Huge The status quo cannot hold.
I hope I've convinced you that the status quo cannot hold. That even people who aren't that privacy- or security-conscious recognize that there are risks not only at a personal level, but also national and global.
Push Back B_fullframe
- Good crypto; no trust
- Lawmakers: this is not something we can win while we fight with our governments.
Thank You B_fullframe
Mike Gerwitz
\bigskip
References Available Online
https://mikegerwitz.com/talks/sapsf
\vfill
Licensed under the Creative Commons Attribution ShareAlike 4.0 International License
References B_appendix
\printbibliography
Exporting
You should be able to simply export this buffer as a Beamer presentation
(C-c C-e l P) and get a slideshow.
Note that this requires ox-extras, which is part of Org Mode's
contrib/. Without it, the :ignore: tag will not be recognized and the
rendered slides will have incorrect depth.